Law enforcement officers today are faced with many new applications that that allow users to communicate or store information privately. As consumers become more concerned with privacy and security, the use of these applications continues to rise. And they aren’t just for criminals or spooks – secure messaging apps have gained widespread popularity among the general populace.
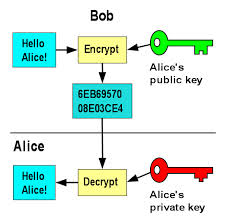
The novelty of these apps is that rather than encrypting only part of a conversation,

 by the
by the