By: Center for Internet Security
The Center for Internet Security (CIS) recently published their monthly Cyber Tips newsletter, The Harm in Password Reuse.
Below is the content provided in the newsletter published by CIS:
From the Desk of Desk of Thomas F. Duffy, Chair
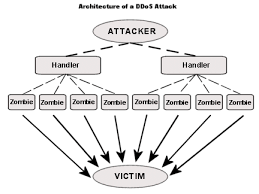
Every day malicious cyber actors compromise websites and post lists of usernames, email addresses, and passwords online.